Trend Micro
Presentation Title What Global Threat Trends Tell About Cyber Risks in Japan
“Know the Enemy”: The First Step in Protecting Your OrganizationUnderstanding the Intention of Attacks for Effective Defense
Yohei Ishihara
Security Evangelist
Trend Micro
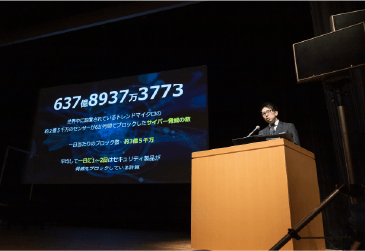
“When we think about cyberattacks, we need to understand both numbers and intentions,” says Yohei Ishihara of Trend Micro. He claims that it is vital to understand attacks not just quantitatively, but also in terms of the motivation that lies behind them.
Cyberattacks can be broadly classified into two kinds, according to their purpose. One is cybercrimes, aimed at financial gain; the other is advanced persistent threats (APTs), aimed at stealing military or diplomatic information, or achieving other subversive objectives. “Currently, the majority of all cyberattacks are cybercrimes; there are very few APTs,” explained Ishihara. There is a big difference between the two kinds.
Nevertheless, APTs cannot be treated lightly because they could cause sabotage, information manipulation, and the like. Once an APT attack occurs, therefore, it can inflict very serious damage.
A useful “victimology” approach to potentially devastating ransomware attacks
Ransomware has become a particularly serious form of cyberattack in recent years. As Ishihara explains, “victimology” offers an effective method of analyzing ransomware trends. “Victimology is a criminological approach to understanding criminals by analyzing their victims. Although there is a tendency to focus on criminals, there are things that can be learned by looking at the victims of crimes.”
An obvious example is the regional characteristics of victims. As we analyze the distribution of the ransomware victims against GDP distribution by region, a comparison between the two of the major strains of ransomware, Conti and LockBit, reveals a stark difference in how each group of attackers operates. As many as 93% of Conti victims are found in North America and Europe with only few victims in other regions, suggesting their extreme regional bias irrespective of the global wealth distribution.
On the other hand, such regional bias is much less extreme with LockBit victims, as the distribution is similar to the distribution of GDP by region. Ishihara added “Please note however that, in the case of Conti as well as LockBit, there have been a relatively small number of victims in the Asia-Pacific region (APAC). This is most likely due to language barriers.”
Ishihara also said “There’s a general impression that ransomware is targeted mainly at large corporations and medical institutions, but no clear patterns of damage by industry are evident. As for the amount of ransom, analysis of the ransom notes delivered to attacked organizations has shown that it is typically around 5% of the annual recurring revenue of the targeted company. These statistical analyses are very useful in understanding the reality. We must be careful not to let ourselves be swayed by our impressions.”
Ishihara’s message is “know your enemies well,” which includes analyzing their victims. He said, “One of the most prominent that we should definitely know better are ransomware attackers. And it is essential to understand that in many cases attackers are structured organizations, not individuals.” In up to 70% of cases, information is not only encrypted, but also stolen and disclosed. “The fact that these attacks can occur indicates that attackers lurk within the networks of victims for a certain amount of time. It is therefore necessary to know the enemy and be prepared to defend against it,” explained Ishihara.
95% of ransomware attacks in Japan are specifically targetedPrevent threats by “connecting the dots”
A key phrase that Ishihara conveys is “see threats as lines, not points.” One of the trends in the ransomware attacks in Japan that we should note is that, since 2018, most are targeted at a specific victim organization. In fact, 95% of the ransomware incident response cases that Trend Micro supported have involved targeted attacks. As Ishihara put it, “The threats come in lines. First there is intrusion, followed by elevation of privileges, then clearing conditions, and finally putting the ransomware in place. Defenders must therefore follow these same lines of defense.”
Unfortunately, international surveys have revealed that many organizations in Japan tend to view each cyberattack as an isolated incident. This means they take each as “a dot” rather than as “part of a line” where possible relations between each are analyzed so that their links can be established. More and more organizations in Europe and North America today have adopted the latter approach. Ishihara warned, “Although defenses are evolving, by international standards Japanese companies are still weak in measures based on evaluating cyberattacks holistically “as lines”.”
To survive a targeted attack, companies must modernize their view on ransomware attacks. We should get past the outdated image of mass attacks where it was common to assume “ransomware does not pose a big threat as long as we don’t open suspicious emails”. It is vital to take a holistic view of threats, with an acceptance that sophisticated ransomware attacks are becoming more prevalent.
“Knowing the threats” can help to determine where efforts need to be directed, Ishihara said. He concluded on a positive note: “My hope is that organizations in Japan will become more eager to gather information so they can learn more about their adversaries. The fact that Japanese companies still don’t do enough to learn about threats means that there is still plenty of defensive measures untapped that could be truly efficacious”
Related Links
Trend Micro
-
Deloitte Tohmatsu Group
Deloitte Tohmatsu’s Emphasis on “Business Compatibility”
The Importance of Cybersecurity Strategy - IBM Japan Attackers Target the Weakest Link, So Build an Optimal Security System Through “Selection” and “Concentration”
-
Trend Micro
“Know the Enemy”: The First Step in Protecting Your Organization
Understanding the Intention of Attacks for Effective Defense - NTT Security Holdings Organizational Strength of Research Teams Help Protect Japanese Companies from Targeted Attacks
- BlackBerry Japan AI Mathematical Models for Better Detection and Protection than Existing EPPs
- Secureworks A New XDR Method to Protect Organizations from Evolving Ransomware Threats
- Sateraito Office Offering Versatile Security Products and Know-How Cultivated from Working with Over 60,000 Companies
- ZenmuTech Two Technologies for Digital Transformation: “Secret Sharing” and “Secure Computation”
- ServiceNow Japan Visualizing IT Systems Using a Configuration Management Database: Asset Management is the First Step to Security
- Darktrace Japan Visualizing Vulnerabilities and Risks with AI to “Autonomously Prevent” Attacks